DataZone
Note: This documentation is also available in a rendered format here.
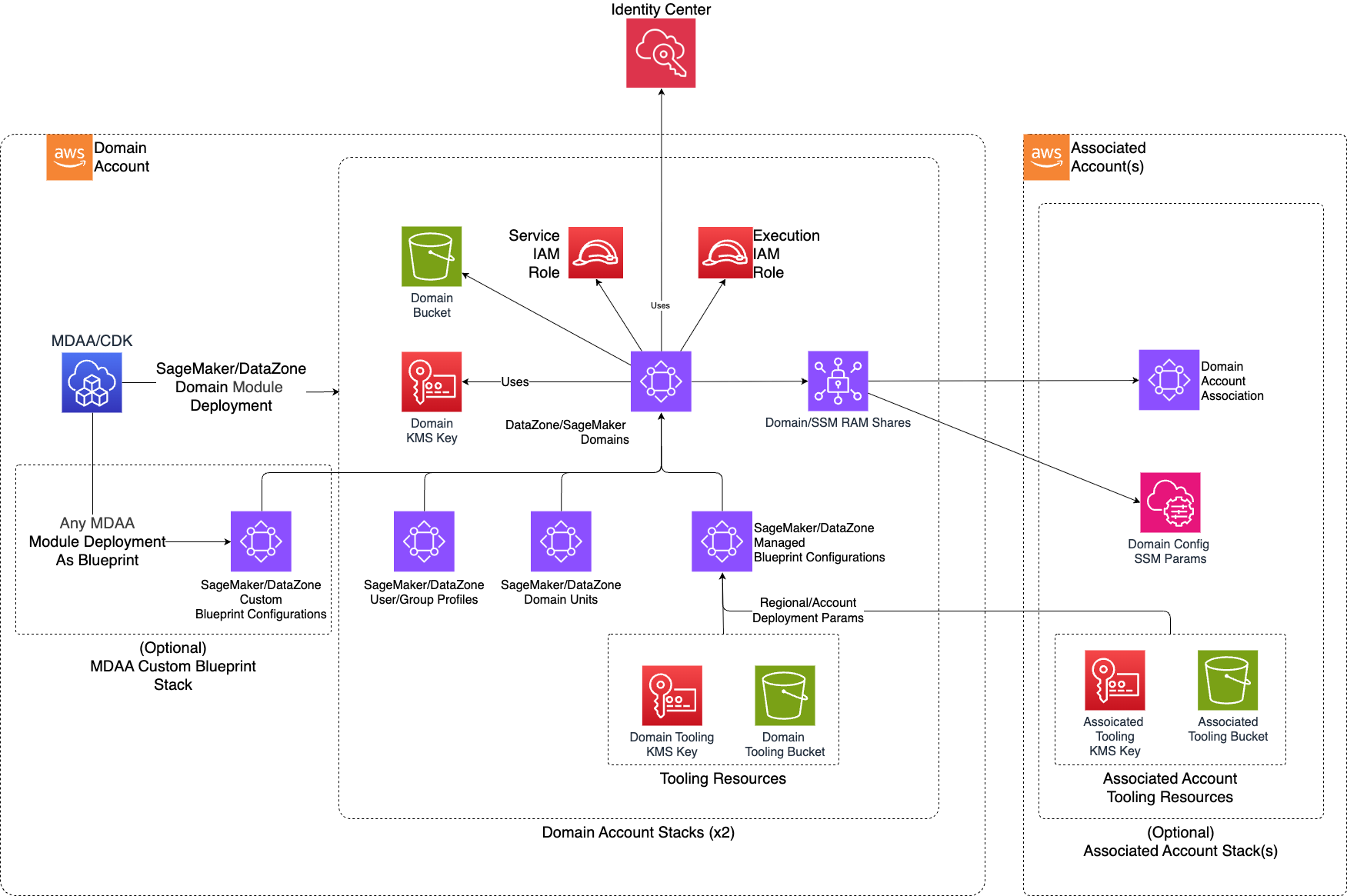
Deploys Amazon DataZone (V1) domains with domain units, user/group profiles, environment blueprints, associated accounts, KMS encryption, and Lake Formation integration for governed data sharing. DataZone V1 is the predecessor to SageMaker Unified Studio. Choose this module if you have an existing DataZone V1 deployment; for new deployments, consider the SageMaker module which provides the latest SageMaker Unified Studio experience with a unified portal for data engineering, analytics, and ML. Use this module when you need a governed data catalog and sharing portal for teams to discover, request access to, and consume data assets across organizational boundaries.
Deployed Resources
This module deploys and integrates the following resources:
DataZone Domain - A DataZone Domain with configurable SSO and user assignment modes.
DataZone Domain Units - Hierarchical organizational units for project creation.
DataZone User/Group Profiles - User/Group profiles for IAM and SSO principals.
KMS CMK - Customer-managed encryption key per domain.
Domain Execution Role - IAM Role used by DataZone, specific to each domain.
Domain Bucket - S3 bucket for domain-specific resources.
Associated Account Stacks - Cross-account resources for multi-account domain access.
Related Modules
- Lake Formation Settings — Configure Lake Formation admin roles required for DataZone domain data governance
- Glue Catalog Settings — Configure cross-account Glue Catalog encryption keys for associated accounts
- Roles — Create IAM roles for DataZone domain user/group profiles
- SageMaker (Domain) — Alternative to DataZone for governed data access and project management using SageMaker Unified Studio
Security/Compliance Details
This module is designed in alignment with MDAA security/compliance principles and CDK nag rulesets. Additional review is recommended prior to production deployment, ensuring organization-specific compliance requirements are met.
- Encryption at Rest:
- Each domain encrypted with a dedicated customer-managed KMS key
- Glue catalog encryption key integration for metadata access
- Least Privilege:
- Domain unit ownership model with user/group-level access
- SSO and IAM authentication modes
- Separation of Duties:
- Lake Formation admin role integration for fine-grained data access control
- Associated accounts with configurable Glue catalog KMS key access and per-account Lake Formation admin roles
Configuration
MDAA Config
Add the following snippet to your mdaa.yaml under the modules: section of a domain/env in order to use this module:
datazone: # Module Name can be customized
module_path: '@aws-mdaa/datazone' # Must match module NPM package name
module_configs:
- ./datazone.yaml # Filename/path can be customized
Module Config Samples and Variants
Copy the contents of the relevant sample config below into the ./datazone.yaml file referenced in the MDAA config snippet above.
Minimal Configuration
Required properties only — a single domain with an admin role. Start here for a basic DataZone domain with a single administrator.
# Contents available via above link
# Minimal DataZone module configuration.
# Contains only required properties for a basic DataZone domain deployment.
# Map of domain names to DataZone domain configurations
domains:
test-domain:
# See CONFIGURATION.md for role reference options (name, arn, id).
# IAM role with administrative privileges over the domain
dataAdminRole:
name: Admin
Comprehensive Configuration
Covers both enum variants, all PolicyType values, nested domain units, cross-account associations, and all principal types. Start here when evaluating all available options for domain units, user/group profiles, environment blueprints, and multi-account governance.
sample-config-comprehensive.yaml
# Contents available via above link
# Comprehensive sample config for the DataZone module.
# Exercises ALL compatible non-excluded properties at full depth.
# Covers both enum variants, all PolicyType values, nested domain units,
# cross-account associations, and all principal types.
# (Optional) KMS key ARN for Glue catalog encryption in this account.
# If omitted, looked up from the standard LF Settings SSM parameter.
glueCatalogKmsKeyArn: test-glue-catalog-key-arn
# (Optional) IAM role for Lake Formation permission management across
# all domains. If omitted, looked up from the standard LF Settings SSM param.
lakeformationManageAccessRole:
arn: 'arn:{{partition}}:iam::{{account}}:role/test-lf-admin-role'
# Map of domain names to DataZone domain configurations (required)
domains:
# First domain: SSO disabled, manual user assignment
test-domain:
# See CONFIGURATION.md for role reference options (name, arn, id).
# (Required) IAM role with administrative privileges over the domain
dataAdminRole:
name: Admin
# (Optional) Human-readable description of the domain
description: DataZone Domain Description
# (Optional) SSO integration type (enum: DISABLED | IAM_IDC)
singleSignOnType: IAM_IDC
# (Optional) User assignment mode (enum: MANUAL | AUTOMATIC)
userAssignment: AUTOMATIC
# (Optional) CDK deployment role ARN for this domain's account. Override when
# using a custom CDK bootstrap qualifier instead of the default.
cdkRoleArn: 'arn:{{partition}}:iam::{{account}}:role/custom-cdk-cfn-exec-role'
# (Optional) Users to be added to the domain (IAM or SSO)
users:
# IAM-based user (mutually exclusive with ssoId)
iam-user-name:
iamRole:
arn: role-arn
# SSO-based user (mutually exclusive with iamRole)
sso-user-name:
ssoId: sso-user-id
# (Optional) Groups to be added to the domain (SSO only)
groups:
test-sso-group1:
ssoId: test
test-sso-group2:
ssoId: test2
# (Optional) Users granted ownership of the root domain unit
ownerUsers:
- sso-user-name
# (Optional) Groups granted ownership of the root domain unit
ownerGroups:
- test-sso-group1
# (Optional) Associated accounts granted ownership of the root domain unit
ownerAccounts:
- associated-account-name1
# (Optional) Simplified authorizations for the root domain unit.
# Provides a concise way to grant common permissions without constructing
# full AuthorizationPolicy objects.
authorizations:
# (Optional) Users/groups allowed to create projects (CREATE_PROJECT policy)
projectCreators:
users:
- sso-user-name
groups:
- test-sso-group1
# (Optional) Users/groups allowed to be added to project member pools
# (ADD_TO_PROJECT_MEMBER_POOL policy)
eligibleProjectMembers:
users:
- iam-user-name
groups:
- test-sso-group2
# (Optional) Users/groups allowed to create child domain units
# (CREATE_DOMAIN_UNIT policy)
domainUnitCreators:
users:
- sso-user-name
# (Optional) Users/groups allowed to create glossaries
# (CREATE_GLOSSARY policy)
glossaryCreators:
users:
- sso-user-name
groups:
- test-sso-group1
# (Optional) Users/groups allowed to create environments
# (CREATE_ENVIRONMENT policy)
environmentCreators:
groups:
- test-sso-group1
# (Optional) Fine-grained authorization policies for the root domain unit.
# Supports all PolicyType values with user/group/account principals.
authorizationPolicies:
root-create-project-policy:
policyType: 'CREATE_PROJECT'
principals:
- userName: iam-user-name
- groupName: test-sso-group1
includeChildDomainUnits: true
root-create-domain-unit-policy:
policyType: 'CREATE_DOMAIN_UNIT'
principals:
- userName: sso-user-name
includeChildDomainUnits: true
# (Optional) Hierarchical domain units for organizing projects
domainUnits:
test-unit1:
# Owners are automatically granted CREATE_PROJECT authorization
ownerUsers:
- sso-user-name
ownerAccounts:
- associated-account-name2
description: testing
# (Optional, Deprecated) Use authorizations.eligibleProjectMembers instead.
# When true, all domain users are added to the project member pool
# (does not grant direct project access).
allowAllUsers: true
# (Optional) Simplified authorizations for this domain unit
authorizations:
# (Optional) Users/groups allowed to create projects (CREATE_PROJECT policy)
projectCreators:
users:
- sso-user-name
groups:
- test-sso-group1
# (Optional) All domain users added to the project member pool.
# Replaces the deprecated allowAllUsers property.
eligibleProjectMembers:
all: true
# (Optional) Users/groups allowed to create child domain units
# (CREATE_DOMAIN_UNIT policy)
domainUnitCreators:
users:
- sso-user-name
# (Optional) Users/groups allowed to create glossaries
# (CREATE_GLOSSARY policy)
glossaryCreators:
groups:
- test-sso-group1
# (Optional) Fine-grained authorization policies
authorizationPolicies:
# PolicyType: CREATE_DOMAIN_UNIT
create-domain-unit-policy:
policyType: 'CREATE_DOMAIN_UNIT'
principals:
- userName: sso-user-name
- accountName: associated-account-name1
includeChildDomainUnits: true
description: Allow creating child domain units
# PolicyType: CREATE_PROJECT
create-project-policy:
policyType: 'CREATE_PROJECT'
principals:
- userName: iam-user-name
- groupName: test-sso-group1
- allUsersGrantFilter: true
# (Optional) Blueprint authorization configuration
blueprintConfig:
includeChildDomainUnits: true
# projectDesignation (enum: CONTRIBUTOR | OWNER)
projectDesignation: OWNER
# PolicyType: CREATE_GLOSSARY
create-glossary-policy:
policyType: 'CREATE_GLOSSARY'
principals:
# userIdentifier with name and identifier
- userIdentifier:
name: sso-user-name
identifier: sso-user-id
# groupIdentifier with name and identifier
- groupIdentifier:
name: test-sso-group1
identifier: test-group-id
# (Optional) Specific domain unit ID to scope the policy
domainUnitId: test-domain-unit-id
# PolicyType: CREATE_ASSET_TYPE
create-asset-type-policy:
policyType: 'CREATE_ASSET_TYPE'
principals:
- userName: sso-user-name
# PolicyType: CREATE_ENVIRONMENT
create-environment-policy:
policyType: 'CREATE_ENVIRONMENT'
principals:
- groupName: test-sso-group1
# PolicyType: CREATE_ENVIRONMENT_FROM_BLUEPRINT
create-env-from-blueprint-policy:
policyType: 'CREATE_ENVIRONMENT_FROM_BLUEPRINT'
principals:
- userName: iam-user-name
# PolicyType: CREATE_ENVIRONMENT_PROFILE
create-env-profile-policy:
policyType: 'CREATE_ENVIRONMENT_PROFILE'
principals:
- userName: sso-user-name
# PolicyType: CREATE_FORM_TYPE
create-form-type-policy:
policyType: 'CREATE_FORM_TYPE'
principals:
- groupName: test-sso-group2
# PolicyType: ADD_TO_PROJECT_MEMBER_POOL
add-to-project-member-pool-policy:
policyType: 'ADD_TO_PROJECT_MEMBER_POOL'
principals:
- userName: sso-user-name
# PolicyType: CREATE_PROJECT_FROM_PROJECT_PROFILE
create-project-from-profile-policy:
policyType: 'CREATE_PROJECT_FROM_PROJECT_PROFILE'
principals:
- allUsersGrantFilter: true
# PolicyType: DELEGATE_CREATE_ENVIRONMENT_PROFILE
delegate-create-env-profile-policy:
policyType: 'DELEGATE_CREATE_ENVIRONMENT_PROFILE'
principals:
- accountName: associated-account-name1
# PolicyType: OVERRIDE_DOMAIN_UNIT_OWNERS
override-domain-unit-owners-policy:
policyType: 'OVERRIDE_DOMAIN_UNIT_OWNERS'
principals:
- userName: sso-user-name
# PolicyType: OVERRIDE_PROJECT_OWNERS
override-project-owners-policy:
policyType: 'OVERRIDE_PROJECT_OWNERS'
principals:
- groupName: test-sso-group1
# blueprintConfig with CONTRIBUTOR variant
blueprintConfig:
includeChildDomainUnits: false
projectDesignation: CONTRIBUTOR
# (Optional) Nested child domain units
domainUnits:
test-unit2:
description: testing
ownerGroups:
- test-sso-group2
# (Optional, Deprecated) Use authorizations.eligibleProjectMembers instead.
# Specific user names added to the project member pool
# (does not grant direct project access).
allowedUsers:
- sso-user-name
# (Optional, Deprecated) Use authorizations.eligibleProjectMembers instead.
# Specific group names added to the project member pool
# (does not grant direct project access).
allowedGroups:
- test-sso-group1
# (Optional) Simplified authorizations for this child domain unit
authorizations:
# (Optional) Users/groups allowed to be added to project member pools
# (ADD_TO_PROJECT_MEMBER_POOL policy)
eligibleProjectMembers:
users:
- sso-user-name
groups:
- test-sso-group1
# (Optional) Users/groups allowed to create environments
# (CREATE_ENVIRONMENT policy)
environmentCreators:
users:
- sso-user-name
# (Optional) Cross-account associations
associatedAccounts:
associated-account-name1:
# (Required) AWS account ID
account: '{{context:account-2}}'
# (Optional) KMS key ARN for Glue catalog encryption
glueCatalogKmsKeyArn: test-associated-glue-catalog-key-arn
# (Optional) Create a DataZone domain user for CDK deployments
createCdkUser: true
# (Optional) IAM role ARN for Lake Formation access management
lakeformationManageAccessRoleArn: 'arn:{{partition}}:iam::{{account}}:role/test-role'
# (Optional) CDK deployment role ARN for cross-account provisioning
cdkRoleArn: 'arn:{{partition}}:iam::{{context:account-2}}:role/test-cdk-role'
# (Optional) AWS region for the associated account resources
region: '{{region}}'
associated-account-name2:
account: '{{context:account-3}}'
createCdkUser: true
lakeformationManageAccessRoleArn: 'arn:{{partition}}:iam::{{account}}:role/test-role'